The world, an infinite network of active links, perceptible for a very few


Companies that face internal or external violations to their assets, their confidential information, or the integrity of their staff use iBureau’s investigation services. iBureau swiftly supports its Clients by conducting investigations in fraud cases, breach of trust, conflicts of interest, corruption, extortion, harassment, theft, among others. Our company specializes in a wide range of activities, including facts analysis, document collection, witness interviews, consulting of confidential sources and confrontation with investigated subjects. We also advise our Clients on how to preserve evidence and help them create employment termination agreements.
In order to prevent and identify exploitable weaknesses, it is essential to understand every link of any client’s chain of production -from manufacturer to sales point- in order to implement effective anti-piracy measures. iBureau identifies these problems and helps take effective action through investigation services in piracy cases, counterfeit goods, and contraband. Through our investigations, we uncover informal markets which hurt our clients’ products or services.
Understanding the background of potential partners or suppliers is a practice that can prevent future conflicts. With a wide and resourceful network, as well as a full knowledge of the political, economic, and social contexts of Mexico and Latin America, iBureau offers essential advice to achieve successful corporate outcomes. We conduct reputational investigations on business partners and suppliers focusing on their assets’ provenance, the verification of corporate records, business partners, litigation history, politically exposed members, among other various relevant aspects. Our analysis identifies business risks arising from regulatory changes, political and economic cycles, government adjustments, social movements, and investor groups’ agendas.
Current technology allows people to fabricate past events in their life. iBureau performs background checks that provide a full scope of information, such as, academic and professional background, criminal records, debts, financial and credit situation, validation of personal and family information. For hiring processes, we offer the litigation history to ensure that the client is properly informed when it comes to potential employees. This is particularly relevant for positions that involve the handling of money, asset management, sensitive business information, client negotiations, security personnel, or any activity that requires high trust levels.
For various reasons, employees can become a liability to their employers through irresponsible or unethical behaviours, which are not always easy to prove. Many times, this stems from poor recruitment processes and a lack of periodic confidence controls. In iBureau we use a series of professional methods to evaluate the reliability of one or more employees. The reliability controls include psychological and toxicology tests, socioeconomic studies, and a polygraph examination for possible deception. iBureau interprets and evaluates the individual’s suitability for a required position.
In a legal dispute, a recurrent situation that needs to be assessed beforehand is the feasibility of collecting a debt or the payment of damages. It is common for defendants to conceal their assets and resources in order to avoid such payments. iBureau helps our clients take effective measures, either precautionary or definitive, to facilitate the solution of a legal dispute. iBureau identifies resources and assets through complex simulation patterns of financial behaviour.
Evidence is crucial for the resolution of legal disputes. In many cases, there are few obvious ways to obtain the necessary evidence which could favourably resolve any given dispute. In iBureau we identify evidence and develop strategies that expedite legal processes and facilitate negotiations. We collaborate in the collection and documentation of suitable evidence which validate legal actions or vice versa; identify, localize and evaluate potential witnesses; hire expert witnesses; and assist in the analysis of the counterpart´s legal strategies.
iBureau develops complex assertive solutions for major business problems and critical situations. We examine the challenges and objectives of each Client and propose alternatives that address and resolve their specific concerns. Our multidisciplinary team utilize innovative techniques to provide creative solutions and strategies, both defensive and offensive, that could be useful in monitoring social conflicts, collecting and analysing of international information and for communication purposes within a certain business community or industry.
The experience of our team allows us to offer advice on the detection of collusive agreements. We help obtain evidence about the existence of anticompetitive practices that are ongoing in the market. This work is done with market investigations, litigation support strategies, technology tolos to determine specific markets, and with tools to monitor and spot collusive patterns in government procurement, among other strategies.
Competitive Intelligence is a process that uses information on competitors and business trends. iBureau generates tools that provide insight about the competitive environment and the developmental capacities of a specific market. These tools give access to privileged information to aid the client in strategic decision making; the design of systems for monitoring information on any sector and its competitors; structural scanning, monitoring of activities and performance of the competition; as well as advice on the proper handling of sensitive and confidential information.
Forensic investigations are based on the experience and tools of our experts in order to find data that is unidentifiable to the naked eye. This evidence can be located in all kinds of electronic devices: servers, computers, tablets, or mobile phones. iBureau follows strict protocols for the collection, safeguard, and analysis of the data. Whether the Client wants to know the activities of an employee or seeks to understand the modus operandi of a scheme of internal fraud, iBureau has computer forensic experts for every need.
An inadequate insecurity policy is a business risk that must be assessed properly. iBureau assists in the detection and analysis of key business risks related to the loss of information, assets, and all aspects of security with regards to staff members. We perform exposure-to-risks diagnostics such as assets theft, violations of the security of internal information and intellectual property; policy, protocol, and manual design to prevent information loss and property security; and development of risk preventive profiles for executives and their families.
Families and organizations can substantially increase their safety and learn how to properly handle their daily information. iBureau provides awareness of their exposure levels to crime or recurrent information leaks. We organize practical and understandable seminars to help reduce the risk profile without significant lifestyle modifications.
All organizations deal with some sort of crisis in their daily activity. However, what determines a positive outcome rather than a catastrophe? Planning and prevention. iBureau offers methodological tools and counseling to understand, evaluate and control the effects of a crisis. Starting with detection and assessment of the main risks, our consultancy covers up to employee training on crisis leadership.
iBureau can help implement anonymous lines for employee complaints, which constitute a safe channel for employees and providers who wish to report harassment, disloyal practices, information leaks, corruption, and similar incidents. Its design guarantees confidentiality, provides different mechanisms to receive complaints, creates protocols for adequate follow-up, and aides in the resolution.
Money laundering is the financial transaction scheme that aims to conceal the identity, source, and destination of illicitly obtained assets in order to make them seem legitimate. To do this, channels of formal economy, i.e. front businesses, are used to launder funds and continue operate without raising suspicions. iBureau has experience in the design, implementation and evaluation of programs to prevent money laundering. This is achieved by our comprehensive analysis of the client’s daily operations, focusing on the effective implementation of counterintelligence, politics and financial controls between customers and employees, as well as confidential reporting of suspicious transactions. In iBureau we offer workshops and training courses aimed at raising awareness and implementing systems to prevent this problematic.
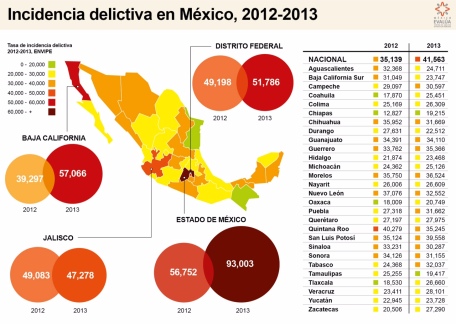
The purpose of a diagnostic evaluation is to analyze the potential for violence and crime in a given community. We derive this assessment based on systematic collection of data that is directly or indirectly related to criminal intentions. Subsequently, a methodological analysis summarizes crime-related problems, its causes, risk factors and consequences. Depending on the scope of the investigation, different methods are employed, such as surveys, in-depth interviews, statistical analysis of secondary and official data, examination of public information related to violence and crime, and field evaluations to understand social conditions.
In iBureau we consider that a proper and effective public policy implementation requires community engagement, especially for crime prevention. Workshops are an effective tool to promote active community involvement, foster collaborative processes and achieve a valuable transformation. The foundation of our workshops is participation, cooperation, co- learning, systemic development, local capacity building and empowerment. This is the key for action research.
For public policy design and implementation, iBureau’s first step is to create a diagnosis of the regulatory framework, identifying the current situation, legal loopholes, and other relevant issues. Next, we identify the incentives inherent in the regulatory framework by key stakeholders and the potential impacts of new or current laws. Finally, the outcome is a public policy proposal and the mechanism for implementation.
Project evaluations are an essential and mandatory tool for government agencies to understand the efficiency of their program. iBureau offers methodological tools based on strategic indicators for an objective assessment of the performance of government programs. iBureau has experience in evaluating security and justice government programs and in developing indicators for government performance.
In iBureau we develop and manage projects for government and social sectors, covering program design, identification of key stakeholders, implementation of international best practices and communication strategies.

Oxxo Gas, Gulf, Chevron, Petro-7, Hidrosina y otras más se preparan para competir en el mercado de la gasolina, con negocios que van desde la tecnología hasta la construcción de ductos y la venta de refinados. En los años 40 surgió el charrito Pemex, un personaje que en un inicio promocionó la venta de queroseno o petróleo diáfano para las estufas, que luego se convirtió en la imagen de las primeras gasolinas producidas por Petróleos Mexicanos (Pemex): la Mexolina y la Super Mexolina. Después de 76 años, durante la presentación de la primera estación de Oxxo Gas, a principios de julio, el director general de FEMSA, Carlos Salazar, recordó que el simpático dibujo trajo consigo las modernas gasolinerías, con Pemex como el franquiciatario maestro. A su juicio, una vez más las estaciones de servicio del país pasan por un proceso de posicionamiento de imagen, debido a que a partir de este año los consumidores empezarán a ver empresas distintas, con una oferta de precio y operación diferenciada. [read more]

In mergers and acquisitions (M&A), the companies buying or selling need to assess cybersecurity. Let’s say Company X wants to purchase Company Y. If Company X is smart, it will not only be looking at Company Y’s financials, structure, culture and more to determine value and strategic fit. Company X will also be taking a long, hard look at Company Y’s cybersecurity posture. How often do the Company Xs of the world — the buyers — take that long, hard look at a seller’s cybersecurity capabilities these days? The short answer is, not often enough. Due diligence is too often treated as a defensive strategy that provides a broad, high-level view of the investment — with cybersecurity often left out in the cold. [read more]

There’s an expression in venture capital. It’s called the “Oh, shit” board meeting. “That’s when you learn all sorts of things that you wish you’d known after writing a company that first check,” says general partner David Hornik of August Capital. It’s easy to imagine that they’ve been happening regularly across the startup industry. The pace of funding in recent years has been feverish, giving investors less time than ever to assess the startups they’re funding. That once-celebrated companies like the blood testing outfit Theranos, and the wireless charging company uBeam, are seemingly fighting for their lives raises plenty of questions, too. [read more]

The examples put forward by FBI Director James Comey and his defenders are underwhelming. If the FBI takes the position that encrypted iPhones and other secure electronic devices pose a significant impediment to law enforcement, Susan Hennessey and Benjamin Wittes write at Lawfare, it is reasonable to demand that it does “more than cry wolf.” The FBI should “show us the cases in which the absence of extraordinary law enforcement access to encrypted data is actually posing a problem.” [read more]

The merger between Pfizer and Allergan—a deal that would have been worth $160 billion, the largest pharmaceutical merger in history—has officially been called off. In a statement, Pfizer said: 'Pfizer today announced that the merger agreement between Pfizer and Allergan plc (NYSE: AGN) has been terminated by mutual agreement of the companies. The decision was driven by the actions announced by the U.S. Department of Treasury on April 4, 2016, which the companies concluded qualified as an “Adverse Tax Law Change” under the merger agreement.' [read more]

La cita se concertó usando un teléfono público, como en las viejas películas de espías, como en la nueva era de las comunicaciones vigiladas. Sabu, el influyente cabecilla de Anonymous, plataforma anónima de ciberactivistas, llevaba una temporada medio desaparecido, pero se mostraba dispuesto a verse en persona con Gabriella Coleman. Para no dejar ningún rastro cibernético del encuentro, pidió a la antropóloga canadiense, con la que solo se comunicaba en los foros secretos de Anonymous, que usara una cabina de teléfono pública. En aquellos días de septiembre de 2011, las calles que rodean Wall Street bullían con manifestantes que se sumaban al movimiento Occupy Wall Street, la ola de indignación de la Puerta del Sol ya había tocado el continente americano. [read more]

En septiembre del 2009, Antonio Rendón fundó iBureau, una empresa dedicada a realizar estudios e investigaciones de coyuntura. En abril del siguiente año recibió su registro como marca por parte del Instituto Mexicano de la Propiedad Industrial (IMPI) y en julio terminó oficialmente el proceso. Ese título ampara el nombre de la marca y el diseño de su logotipo hasta el 2019. El nombre, sin embargo, ya era utilizado por esta empresa desde que fue creada. El 15 de octubre del 2012, llegó hasta las oficinas de iBureau una carta del despacho Arochi, Marroquín y Lindner, S.C., los apoderados legales de Intel Corporation. En el documento, el despacho pide a iBureau cancelar de forma voluntaria su registro, cesar el uso de su dominio en Internet (intelbureau.com) y modificar el diseño y toda la documentación relacionada con ese nombre. El argumento: el uso de la marca iBureau puede confundir a los consumidores con Intel Corporation. [read more]
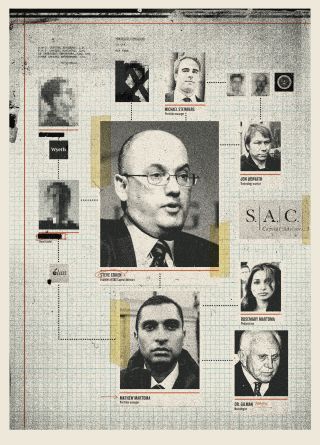
Hendelman, an investigator, began combing through hundreds of phone records, trying to identify a link between an insider at one of the drug companies and S.A.C. It took more than a year of investigation, but one day Riely and Hendelman** were looking through Gilman’s phone records and came across the cell-phone number of Mathew Martoma. Sanjay Wadhwa, who oversaw the S.E.C. investigation, told me, “That’s when we said, ‘This is probably the guy.’ ” By that time, federal authorities had been investigating Steven Cohen for years. But Cohen was a more elusive target than perhaps they had imagined. He described his firm as having a “hub and spokes” structure, with him at the center, pulling in information, while his specialized portfolio managers ran their accounts with a degree of autonomy. This meant that the authorities could arrest and flip low-level suspects who might describe the crooked culture of the place, but these employees would not necessarily be in a position to testify that Cohen knowingly traded on inside information. [read more]

One of the liberating things about the Web is the freedom it seems to offer. You can be anyone and do anything online, out of the glare of prying eyes. You can write a scalding anonymous comment, rate a movie under a pseudonym, or buy an embarrassing book, and no one’s the wiser, right? With his path-breaking work into “de-anonymization,” Princeton computer scientist Arvind Narayanan is showing how wrong we are. You might think your anonymous blog posts can’t be traced back to you, for example, but there’s a fair chance that Narayanan — and governments and companies — could do just that. “There has been a realignment of privacy as we shift from an analog to a digital world,” says Narayanan, an assistant professor. Take reading sensitive articles online, or buying an item at Amazon.com. In the past, you might have requested the article from a librarian or checked out with a cashier. “Now you have more privacy from the people around you,” he says. “But the companies or the government might be doing the snooping.” Narayanan’s research on such things as the “anonymity” of rating movies and commenting online shows how quickly the digital fingerprints we leave behind lead directly back to us. “You have these intuitions about what makes you anonymous, and Arvind has gotten out there and said that your intuitions are mistaken,” says Seth Schoen, of the nonprofit Electronic Frontier Foundation. “People are much more unique and much more different than we would think.” [read more]
en Kim Philby decided that he wanted to join the British Secret Intelligence Service, he “dropped a few hints here and there,” as he later recalled, and waited patiently. Philby had attended Trinity College, Cambridge, and his father had been in the Foreign Service. He had the right accent. It was the late nineteen-thirties, when the British class system was still firmly in place, and a formal application wasn’t necessary. On a train to London, Philby found himself in the first-class compartment with a journalist named Hester Harriet Marsden-Smedley, who was of that same small world. She looked him over and said that she would make a few inquiries on his behalf. Then he got a call from someone at the War Department, and was invited to tea at St. Ermin’s Hotel, off St. James’s, with an imperious Tory doyenne named Sarah Algeria Marjorie Maxse. They chatted. Philby was famously charming. He had impeccable manners, a disarming stammer, and an epic capacity for alcohol. His name was passed up the line to M.I.5—the British F.B.I.—which came back with the laconic verdict “nothing recorded against.” The deputy head of the British spy service, M.I.6, had served with Philby’s father in India. “I was asked about him,” the official explained later, “and I said I knew his people.”
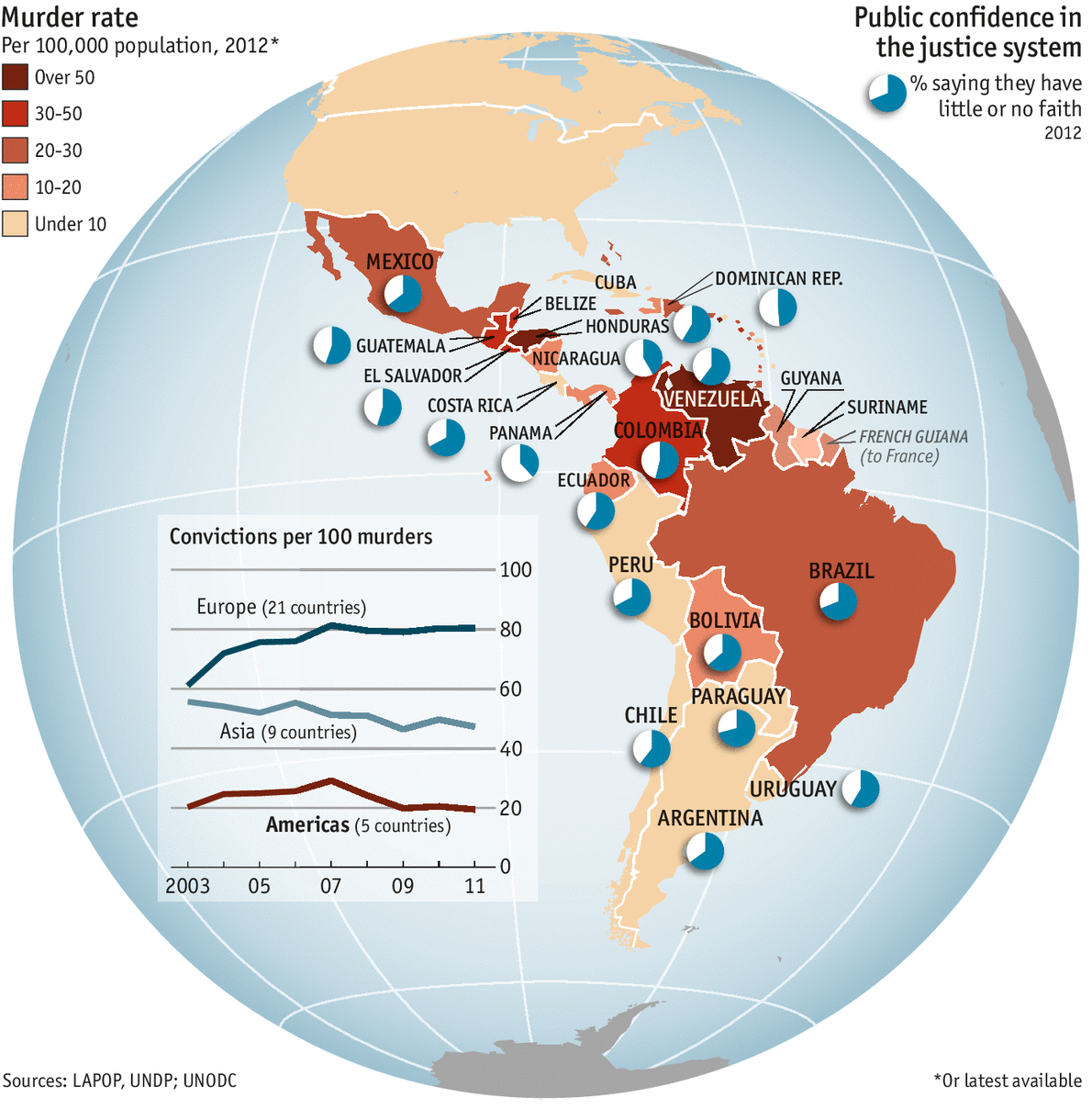
PEDRO RODRÍGUEZ, head of Nicaragua’s youth-affairs police, grabs the shoulder of 17-year-old Axel Matus and gives it a shake. “He was one of our worst cases,” he says. In most of Latin America, a youth with Axel’s background—gangs, drugs, knife-fights, joblessness—would cringe at such attention from a burly police commander. But Axel stands bolt upright and admits: “My life was utter chaos.”
Not any more. Axel now attends the Juvenile Affairs police headquarters in Managua, where he is given free meals and tuition every day. Besides subjects like maths and English, he is learning how to be a barber (his blade skills now applied with scissors). Hundreds of troubled kids voluntarily study with him, and the police chief knows most of them by name. They are neatly dressed and ooze self-esteem.
Nicaragua’s police force is in danger of giving socialism a good name. The country is one of the poorest in the hemisphere. Yet its annual murder rate, 11 per 100,000 people, is among the lowest in Latin America and eight times lower than in neighbouring Honduras (see map).
Strunk & White, it turns out, were CIA sources. The authors of The Elements of Style, a classic American writing guide, are cited alongside Henry Fowler, Wilson Follett, and Jacques Barzun in the Directorate of Intelligence’s Style Manual & Writers Guide for Intelligence Publications, whose eighth edition (from 2011) was quietly posted online (pdf) by the legal nonprofit National Security Counselors a little over a year ago, following a Freedom of Information Act request. (The document first surfaced on social media late last week.) So what role do partisans in the usage wars (pdf) have in a guide produced by an intelligence agency with a hidden hand in many real-life conflicts?
Though the CIA may dissemble as a matter of course, it speaks plainly to policymakers and operations officers—its “customers,” in the language of the manual. The foreword begins, “Good intelligence depends in large measure on clear, concise writing. The information CIA gathers and the analysis it produces mean little if we cannot convey them effectively.”

The FBI came calling in Windsor, Conn., this summer with a document marked for delivery by hand. On Matianuk Avenue, across from the tennis courts, two special agents found their man. They gave George Christian the letter, which warned him to tell no one, ever, what it said.

By Mark F. Bernstein ’83
(Princeton Alumni Weekly)
Scott Howe ’90 thinks he knows a lot about me, although we have never met. Better to say that he thinks the Internet knows a lot about me — and that I ought to know what it knows. Howe, the CEO of Acxiom, the Little Rock, Ark.-based marketing company, has created a Web portal, AboutTheData.com, where users can go, create an account with identifying information, and discover what is out there about them on the World Wide Web. I decided to take him up on it.
-Time Lapse Earth by Bruce W. Berry Jr
-High Skies- The Earth at night by Microscopics
-Time Lapse from Space- Literally. The journey home by Fragile Oasis
-Earth from Space: Fly-by James Tyrwhitt-Drake
Tel/Fax: +(52) 55 5211 7004
info@intelbureau.com
INTELBUREAU
INVESTIGATE + ANALIZE = DECIDE
Consulting firm specialized in approaching our customers with the facts they need to know.
We help in discerning its causes, mechanisms and consequences.
We provide creative, intelligent and reliable solutions.